Organizations continue to struggle with standing admin rights—a long-standing security risk that refuses to go away.
- Remove standing admin privileges → disrupt productivity
- Keep local admin access → increase exposure to cyber threats
This trade-off defines modern endpoint security challenges.
Why Standing Admin Rights Still Exist
Despite the known risks of local admin privileges, organizations rely on them for operational efficiency:
- Reduce IT helpdesk workload
- Enable developer productivity
- Support legacy applications requiring elevated access
- Ensure business-critical apps function without restrictions
In distributed and remote environments, standing admin rights often become the default, not the exception.
Why Standing Admin Rights Are a Security Threat
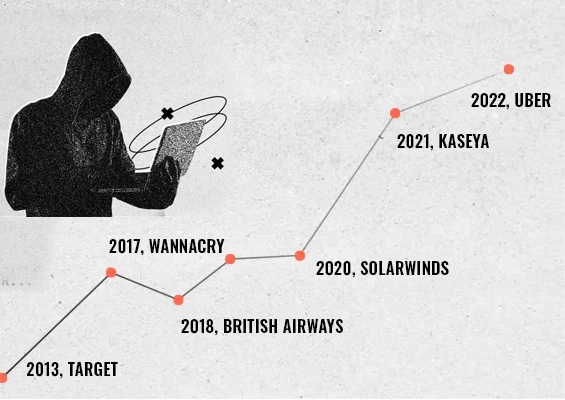
Modern attackers actively target endpoints with standing admin privileges. Admin privileges open up multiple attack pathways that would not be available otherwise. Some of the most common methods used in 2026 that leverage admin rights are explained below.
1. Privilege Escalation and Credential Theft
When an endpoint becomes compromised, the first thing intruders look for is accounts with administrator rights and delegated permissions. They do that because, admin rights make it easier for attackers to:
- Escalate privileges
- Move laterally across systems
2. EDR Evasion (EDR Silencing)
Typically, organizations employ endpoint detection and response tools for detecting intruders in the IT network. Attackers leveraging kernel level access and legitimate system processes using admin rights to:
- Disable endpoint detection systems
- Manipulate firewall rules
3. Living-off-the-Land Attacks (LOTL)
Living off the land attacks are carried out by leveraging the permissions carried by local admin accounts to misuse trusted, pre-installed software and processes like PowerShell, Windows Management Instrumentation (WMI), and remote management utilities to perform malicious actions without introducing any foreign malware. The permissions inherited from admin accounts allow intruders to stay undetected.
Using trusted tools like PowerShell, attackers:
- Execute malicious code
- Avoid detection
4. Ransomware Amplification
Ransomware attacks have evolved, and the attackers now employ double extortion methods. Using local admin rights, the attackers can:
- Delete backups
- Encrypt systems
- Access Active Directory and encrypt multiple IT assets in the network.
Local admin rights turn a single compromised endpoint into a network-wide breach vector.
Why Removing Standing Admin Rights Breaks Productivity
Eliminating standing admin rights is not a straightforward ordeal. Many teams and individuals need admin rights to run legacy applications and update their software. Developers need permission to install apps and scripts as part of their job. Removing admin rights from endpoints without addressing these use cases will lead to
1. Increased IT Support Tickets
Users lose autonomy → IT becomes a bottleneck.
Users raising multiple admin access tickets will clog the helpdesk. IT helpdesk will be stuck in firefighting these requests instead of using their time to progress with more meaningful tasks. Users will also become increasingly dependent on the helpdesk for rudimentary tasks.
2. Application Compatibility Issues
Many apps fail without admin privileges, especially legacy systems. Solutions like ERP, SCADA systems, and healthcare applications cannot function without admin rights as they often write directly to protected directories like C:\Program Files and modify the registry key.
These solutions were developed at a time when security policies were lax, and the potential downside was limited.
3. Developer Workflow Disruption
Developers need admin access for:
- Installing tools
- Managing environments
- Running builds
Removing admin rights directly without providing developers with a way to get the job done will cause rifts between the developers and the IT security team in the organization.
Developers cannot do their job effectively without admin rights.
4. Complex Policy Management
Removing admin rights at scale introduces policy management hiccups and complexities. Teams have complex structure and ensuring standing admin rights are removed from all endpoints requires accuracy at scale.
IT teams struggle with:
- GPO complexity
- Administrative overhead
5. Reduced User Productivity
Simple tasks now require IT intervention → operational friction
Basic tasks like updating existing software will require admin rights. When users are forced to raise tickets with the IT helpdesk for every small need, their productivity tanks and operations come to stand still.
The Core Problem with Standing Admin Rights
Organizations continue to rely on standing admin privileges not because they are secure—but because:
- Common alternatives like LAPS are inefficient
- Standard user permissions are insufficient for teams to fulfill their job responsibilities.
This creates a false binary between Security and Productivity
Conclusion
Standing admin rights:
- Expand the attack surface
- Enable advanced cyberattacks
- Increase organizational risk
But removing them outright:
- Breaks workflows
- Slows teams down
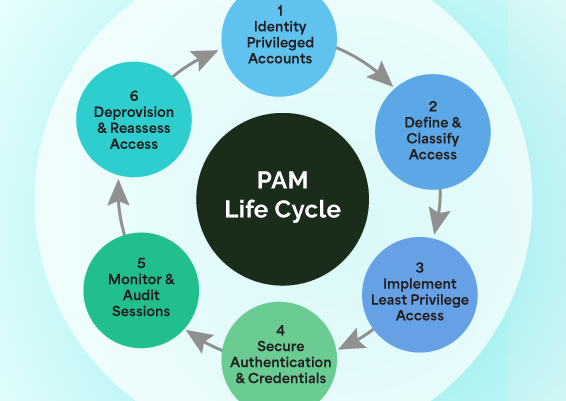
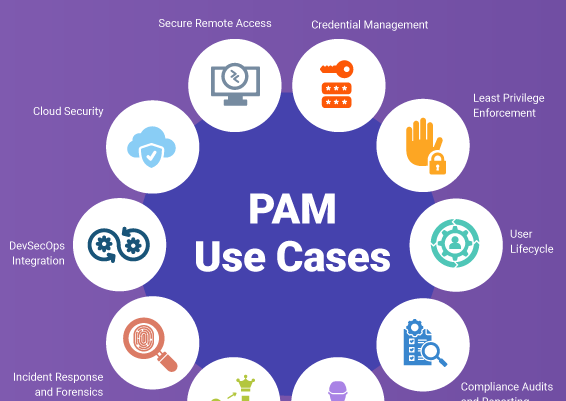
To solve this, organizations must move beyond static privilege models toward the principle of least privilege using Just-in-Time Admin Rights. Let’s discuss least privilege and just-in-time admin rights in the next part.





























![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)